Introduction
Businesses that want to process card payments need to comply with the Payment Card Industry Data Security Standard (PCI DSS).
The PCI DSS lists organizational, technical, and procedural requirements a company must adopt to protect cardholder data.
Each of the 12 PCI DSS requirements has multiple sub-requirements that provide a rundown of specific data control measures and testing procedures.
Get an instant overview of PCI compliance requirements using this convenient checklist.
Disclaimer: This article provides a broad overview of the Payment Card Industry Data Security Standard (PCI DSS). It should not be considered as an official guide for achieving PCI compliance.
1. Install and Maintain a Firewall
A firewall is a security device or software solution that controls incoming and outgoing network traffic. Firewalls are essential for protecting servers, network devices, and applications within the cardholder data environment (CDE).
Note: The Cardholder Data Environment (CDE) consists of system components, staff, and policies that facilitate the collection, processing, or transfer of cardholder and authentication data.
By implementing a comprehensive firewall solution, merchants can:
- Restrict and monitor inbound and outbound traffic to the CDE.
- Deny access to critical system components from public networks.
- Prevent unauthorized outbound traffic.
- Synchronize firewall and router configurations across all systems.
- Place firewalls between wireless access points and systems that process cardholder and authentications data.
- Configure demilitarized zones (DMZ) and ensure that there are no CDE components within the DMZ.
- Introduce measures that prevent DNS spoofing.
- Install personal firewalls on all mobile devices used to access the CDE.
Organizations that want to process card payments should also:
- Document their policies for approving and testing firewall and router configurations.
- Create network diagrams that show all connections between system components that handle cardholder data and public networks (including all wireless access points).
- Use diagrams to display cardholder data flows throughout systems and networks.
- Define and document the responsibilities, roles, and groups in charge of network management.
- Implement firewalls for each internet access point and between the demilitarized (DMZ) and internal network zone.
- List protocols, ports, and services, including the justification for their implementation.
- Review and revise firewall settings and procedures every 6 months.
Merchants can also utilize firewalls and routers to isolate critical system components from the wider network. Network segmentation reduces the scope of a PCI assessment and can keep PCI-related costs under check.
2. Do Not Use Vendor-Supplied Defaults
Default user accounts and passwords supplied by third-party vendors are vulnerable and likely already compromised. Before installing third-party systems and software solutions, merchants should:
- Change all passwords supplied by third-party providers.
- Disable and remove all default user accounts.
- Change vendor default settings on all wireless devices.
- Adhere to industry standards when configuring system components.
- Remove unnecessary scripts, protocols, and other functionalities from vendor solutions.
- Use strong encryption to secure admin access from remote devices.
- Maintain an up-to-date inventory of third-party components in contact with the CDE.
Password policies and configuration requirements for vendor-supplied components need to be well documented and made available to employees. Staff should undergo extensive training and be able to reference the documentation while performing everyday tasks.
3. Protect Stored Cardholder Data
By hashing, encrypting, and truncating collected cardholder data merchants can prevent potential attackers from reading sensitive information even if they manage to bypass other security controls.

All collected cardholder data needs to be encrypted. Merchants also need to ensure that they:
- Only store the minimum amount of data required for conducting business activities.
- Keep historical data stored only for as long as it is necessary.
- Do not store authentication data like the CVV, card chip data, or customer PINs.
- If the customer's personal account number (PAN) needs to be displayed, it should always be masked. Only the first 6 and last 4 digits of the PAN may be shown.
- Hash, truncate, or encrypt stored personal account numbers (PAN).
- Document procedures for protecting the cryptographic keys used for encrypting cardholder data.
Procedures and policies regarding the encryption of stored cardholder data must be documented and made available to all relevant parties.
4. Encrypt Cardholder Data Transmissions
The PCI data security standard prohibits the transfer of unencrypted cardholder data over public networks.
Attackers may intercept and steal data or target vulnerable systems to gain privileged access to the CDE.
To protect data transfers over open networks, merchants should:
- Implement strong cryptography and data transfer protocols.
- Use industry best practices for strong encryption to secure exposed wireless networks.
- Not share unprotected PANs using messaging services, like chat services, emails, or SMS.
The policies and technical procedures for encrypting data transfers need to be written down and accessible to employees.
5. Use and Routinely Update Anti-virus Software
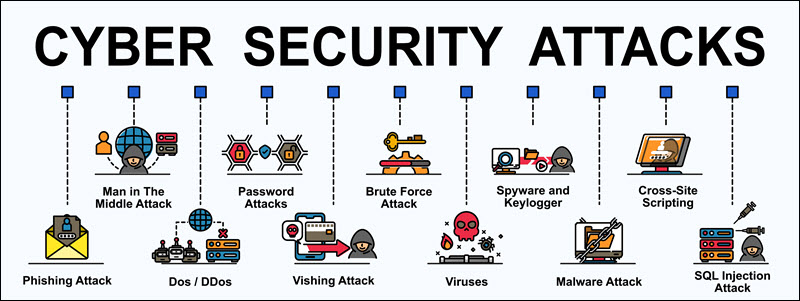
Businesses encounter malicious software like viruses, worms, and Trojans every day. To protect the cardholder data environment from different types of malware, merchants are expected to:
- Deploy anti-virus software on all system components and solutions.
- Ensure that the automated anti-virus software can deal with common malware threats.
- Perform periodic evaluations on other systems that are not under direct threat from malware.
- Keep all anti-virus solutions up to date and conduct periodic scans.
- Ensure that the anti-virus is running at all times and cannot be disabled by unauthorized users.

Staff needs to be given access to official company documentation that outlines anti-software configurations, policies, and employee responsibilities.
6. Develop and Maintain Secure Systems and Applications
To develop and maintain secure systems and applications, in line with payment card industry standards, merchants need to:
- Establish procedures to identify and classify known vulnerabilities into different categories based on their threat level (high, medium, low).
- Protect system components from known vulnerabilities by installing vendor-supplied security patches. Critical patches should be applied within a month of their release.
- Apply strict InfoSec policies throughout the development process when creating custom applications.
- Remove test and development users before custom applications are released.
- Review the custom code prior to release to identify potential vulnerabilities.
It is essential to follow strict security procedures whenever new solutions and components are introduced to the CDE:
- The test and development environments need to be kept separate from active components.
- The roles, users, and responsibilities in the development and test environments need to be kept separate for regular users.
- Cardholder data should not be used for testing purposes.
- All test users need to be removed before a new solution becomes operational.
- Once a change comes into effect, all documentation and procedures need to be updated to reflect the modifications.
The system needs to be strengthened to withstand common vulnerabilities that affect the coding process. These include:
- Injection flaws like SQL injection.
- Buffer overflows.
- Unencrypted or insecure data storage.
- Failure to encrypt data transfer over unencrypted networks.
- The failure to properly handle errors.
- Cross-site scripting.
- Poorly implemented access control measures.
- Cross-site request forgery.
- Broken authentication.
Merchants also need to ensure that all public-facing applications are regularly updated and protected from known threats and vulnerabilities. All documentation outlining these procedures needs to be readily available to designated staff.
7. Restrict Access to Cardholder Data
Only individuals that need cardholder data to complete their work-related tasks should be given access to the CDE. Merchants can limit employee access to cardholder data by:
- Deciding how much and what type of data a specific role requires and restricting all other privileges.
- Defining different levels of user privilege.
- Setting access control systems to deny-all by default and awarding privileges based on role.
- Giving each privileged user the least access rights they need to do their job.
- Defining every individual job, classification, and function in the CDE.
- Providing access only to users who receive written approval from authorized individuals within the organization.
The procedures regarding access controls need to be documented, up-to-date, and available to all relevant parties.
8. Assign Unique ID to Each Person With Access
Assigning an ID to each individual who has access to cardholder data increases personal accountability. Additionally, unique IDs allow merchants to track and register user-initiated events in the CDE. To create a comprehensive user identification management policy:
- Merchants should create unique IDs for each privileged user.
- Credentials need to be regulated, modified, and deleted when necessary.
- Access for terminated users should be revoked immediately.
- Inactive user accounts should be removed after 90 days.
- If users for third-party services access the CDE, they need to be monitored at all times.
- The number of unsuccessful login attempts needs to be limited to 6.
- The default lockout duration should be at least 30 minutes or until an administrator removes the lockout.
- All sessions that have been idle for more than 15 minutes must be re-authenticated.
Merchants should also implement multi-factor authentication and additional verification methods for users accessing the CDE remotely.
- Verify the user's identity utilizing strong authentication methods before allowing any modifications to the credentials.
- Enforce a strong password policy that requires alphanumeric passwords consisting of at least 7 characters.
- Employees must change passwords every 90 days.
- The new password needs to be unique and cannot be the same as the previous 4 passwords for the same user.
- System passwords for the initial login need to be unique, and users must be required to change them during the first login.
- Physical devices like login tokens cannot be shared and need to be assigned to a specific individual.
The password policies need to be well-documented and help employees create robust passwords, and explain why it is essential to avoid generic or weak passwords.
9. Restrict Physical Access to Cardholder Data
Physical access to devices that contain cardholder data, or can provide entry to cardholder data, like wireless access points, needs to be controlled. Merchants should consider implementing physical and logical entry controls like video cameras, employee pass-cards, or PINs.

Merchants need to set up procedures to differentiate between visitors and in-house personnel. These procedures must ensure that:
- Visitors are authorized before entering a facility and are escorted at all times.
- Visitors should be identified and differentiated from employees by, for example, giving them a badge.
- Visitors need to leave the badge when leaving the premises.
- A log of the visitor's activity needs to be kept.
All physical media needs to be secured, backed up, and its distribution strictly controlled. Media that contains cardholder data needs to be shredded, incinerated, or pulped once it's no longer needed. Merchants must ensure that the data cannot be recovered from the destroyed physical device or paper.
A list of physical devices needs to be maintained, and the device surfaces need to be periodically checked for potential tampering.
All the policies need to be written down made available to relevant staff.
10. Track and Monitor Access to Network Resources and Cardholder Data
It is essential to set up an automated system for tracking access to cardholder data. Merchants should implement audit trail links to register all access to system components. The system should log:
- Every individual attempt to access cardholder data.
- Any action taken by a particular user.
- Any action taken by a user with root or administrative access.
- Any attempted access to audit trail logs.
- Invalid access attempts.
- Modifications to user accounts.
- Changes to the function of the audit logs system.
- The creation and deletion of system-level objects.
Merchants can protect audit trails from potential modification by creating log backups, limiting access to trails, and monitoring the integrity of log files. To be effective, records should contain the following information:
- User ID
- Type of event
- Date and time of the event
- Success or failure of the attempted action
- The originator of the event
- Name of the affected system
Merchants can use these logs to identify anomalies or exceptions in all system and CDE components.

The audit history logs should be retained for at least one year, while the last three months need to be on hand for easy access.
Merchants also need to ensure that all critical systems have the correct time and date and that they are synchronized with industry standards.
The audit trail log policy needs to be written down and available to all employees.
11. Routinely Test Security Systems and Processes
Organizations need to implement processes to test for the presence of authorized and unauthorized wireless access points. Merchants should:
- Maintain an inventory of wireless access points.
- Implement incident response procedures.
- Run internal and external vulnerability scans at least every quarter.
- Qualified personnel should perform quarterly internal vulnerability scans.
- Perform scans after changes in network settings.
- Use intrusion detection and intrusion prevention techniques.
Merchants should also develop methodologies for penetration testing:
- This includes external penetration testing by hiring specialized third-party providers.
- Internal penetration testing.
- Exploitable vulnerabilities need to be fixed once detected, and then a test should run again.
- Network segmentation needs to be tested to ensure that there were no changes that reduced security levels.
- Deploy a change detection mechanism and develop procedures for how to react if a change is detected.
Testing procedures must be well documented and accessible to employees conducting penetration tests and vulnerability scans.
12. Implement and Maintain an InfoSec Policy for All Personnel
Merchants need to make sure that all employees adhere to the official company security policy. The policy should be reviewed annually or when changes within the CDE occur. A comprehensive risk-assessment analysis that identifies critical assets and threats must be performed at least once a year.

The security policy should list information security responsibilities for all personnel and:
- Identify technologies whose usage requires approval from authorized individuals.
- Define the type of authentication required for the use of sensitive technologies.
- List all devices and personnel with privileged access.
- Define a method to identify which users triggered events in the CDE.
- List acceptable network access locations.
- Contain a registry of company-approved products.
Organizations should designate individuals responsible for enforcing the usage policy. These employees are expected to:
- Establish, document, and distribute policy documentation.
- Monitor and analyze security alerts.
- Administer user accounts.
- Monitor and control access to user data.
- Distribute security incident response plans and escalation procedures.
- Implement a formal security awareness program and annual security training workshops.
- Ensure that staff formally acknowledges that they have read and understood InfoSec policies.
If an organization uses the services of a third-party provider, it needs to:
- List service providers and what services they provide.
- Have written agreements with third-party providers where they acknowledge that they are responsible for protecting mutual cardholder data.
- Establish a formal process for engaging service providers.
- Maintain a program to monitor service providers.
- Specify which provider is responsible for which PCI DSS requirement.
Merchants also must implement an incident response plan that defines:
- Roles, responsibilities, and communication strategies in case of a data breach.
- A business recovery process.
- A data backup process.
- An analysis of legal requirements.
- Designated personnel that needs to be available 24/7 in case of an incident.
- Training programs that specifically address breach procedures.
- Processes to modify and evolve response plans according to lessons learned.
Potential employees need to be screened prior to their hire. This includes contacting previous employers or checking if the employee has a criminal record.
Conclusion
Merchants that want to implement and sustain the required PCI standards and regularly pass annual PCI assessments need to plan for the long run.
PCI data security standards need to be integrated into their everyday business activities and become an integral part of the overall security strategy.
