Introduction
Customers willingly share personal information and payment card details when buying a product or registering for a service. They trust the payment process and believe that businesses are going to protect their data vigorously.
To secure cardholder data, organizations must implement policies and technical solutions that mitigate risk and actively counter fraud and other security threats. A business that wants to process card payments needs to comply with the Payment Card Industry Data Security Standard (PCI DSS).
Learn about PCI DSS and why complying with its requirements makes card payments more secure.
Disclaimer: This article serves as a general overview of the Payment Card Industry Data Security Standard (PCI DSS). It provides general guidelines and should not be considered as an official guide for achieving PCI compliance.
PCI Compliance Definition
The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements and security assessment procedures intended for organizations that collect, transmit, and process sensitive cardholder information.
PCI DSS outlines the minimal data security measures banks, merchants, and other third-party providers must implement to ensure that cardholder and authentication data is not compromised.
Organizations need to meet PCI DSS requirements and pass a PCI assessment to be considered PCI compliant.
Depending on their compliance level, merchants are asked to submit a Report of Compliance (ROC) issued by a Qualified Security Assessor (QSA) or to complete a PCI Self-Assessment Questionnaire (SAQ).
The acquirer (merchant's bank) reviews the submitted ROC or SAQ, confers with the relevant card brands, and authorizes the merchant to process card payments.
Is PCI Compliance Required by Law?
Payment card brands (Visa, Mastercard, American Express, Discover, and JCB) enforce PCI DSS to make sure that all participants in the payment process have an effective and consistent data security strategy.
The PCI DSS and supporting documents are published and regularly updated by the PCI Security Standards Council (SSC). The PCI SSC is not a government agency, and PCI compliance is not a legal obligation.

International and local laws may compel businesses to implement additional policies and technical solutions for handling cardholder data and personally identifiable information (PII). Such laws and regulations take precedence over PCI data security standards.
PCI DSS Compliance Levels
PCI DSS is a global standard and applies to all organizations that handle cardholder data. However, businesses vary in size and have different business models and organizational capabilities.
Major card brands, like Visa and Mastercard, enforce PCI compliance in coordination with acquiring banks. Merchants are segmented into four (4) levels to streamline the assessment process. The 4 PCI compliance levels are based on the number of card transactions a merchant processes annually.
The level determines the type of assessment a merchant needs to complete during a PCI audit.
| Card Transactions Per Year | Annual PCI Assessment | |
|---|---|---|
| Level 1 | 6 million+ | The audit must be performed by a Qualified Security Assessor (QSA). The QSA issues an official Report on Compliance (ROC) that is submitted to the merchant's bank |
| Level 2 | Between 1 million and 6 million | Self-assessment using a Self-Assessment Questionnaire (SAQ). The form is completed by an employee who is a certified Internal Security Assessor (ISA). Providing a ROC may be a requirement for certain Level 2 businesses. |
| Level 3 | Between 20 000 and 1 million | Self-assessment using the appropriate SAQ form. |
| Level 4 | Fewer than 20 000 | Self-assessment using the relevant SAQ form. |
There are 9 types of PCI compliance Self-Assessment Questionnaires.
Determining which questionnaire to use depends on the organization's business model and how it plans to handle cardholder data. Merchants need to check with their bank or payment card brand to confirm the type of SAQ they need to complete.
Note: Unlike PCI DSS, KYC requirements may differ depending on the country or region. Learn more about KYC (Know Your Customer) in our article What is KYC?
PCI Compliance Requirements
The PCI Data Security Standard defines 12 essential requirements for building and maintaining a secure network, detecting system vulnerabilities, and setting up robust access control practices.
It contains recommendations for implementing the necessary standards and outlines relevant testing procedures to assess their effectiveness.
PCI compliance is an open-ended process that compels merchants to integrate PCI requirements into their everyday business activities.
Install and Maintain a Firewall
A firewall is a security device or software solution that monitors and controls incoming and outgoing network traffic. Firewalls protect internal computer networks from unauthorized external access and malicious attacks.
Network connections between system components that handle sensitive data and untrusted public networks must be restricted and, in some cases, prohibited. It is essential to document cardholder information flows and devise explicit firewall and router configuration procedures and standards.
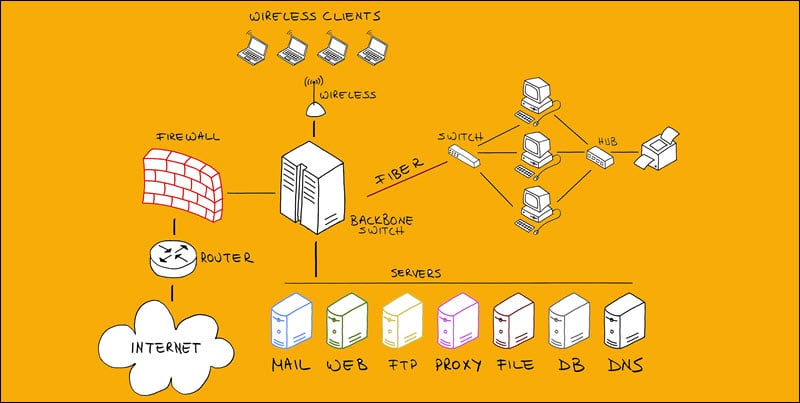
Portable devices with internet access, like laptops or smartphones, should also have personal firewalls if employees use them to access the cardholder environment.
Employees should undergo continuous training to recognize potential threats and follow appropriate security standards when setting up and managing firewalls.
Do Not Use Vendor-Supplied Defaults
Using default system passwords supplied by a vendor is a major security lapse. Such passwords are likely already compromised and are an easy target for brute-force attacks.
All default passwords for system users, devices, and software solutions need to be replaced with strong and unique passwords.
Default user accounts should be permanently disabled before installing a new system. Otherwise, a malicious attacker may reactivate the disabled account and use it to access vital system components.
Instructions and procedures for removing vendor-supplied default users and passwords need to be well documented. Employees can use these guidelines as a valuable resource when creating and updating system passwords.
Encrypt Stored Cardholder Data
Businesses should avoid storing unnecessary cardholder data whenever possible. Stored cardholder information needs to be encrypted, masked, hashed, or truncated. Data encryption prevents potential attackers from reading or using stolen data without the corresponding cryptographic key.
| Cardholder Data | Authentication Data |
|---|---|
| PAN - Personal Account Number | CVV |
| Cardholder Name | PIN |
| Expiration Date | Magnetic Stripe Data |
| Service Number | Card Chip Data |
Merchants need to create a formal policy that outlines rules for collecting and storing cardholder and authentication data. The policy must contain time frames and procedures that explain how to safely and permanently erase cardholder information once it's no longer needed.
Encrypted authentication data should be deleted as soon as the authorization process is complete.
Encrypt Cardholder Data Transmissions
Sending unencrypted cardholder data over public networks is exceptionally risky. Attackers use different techniques, like man-in-the-middle attacks, to intercept and steal data. Businesses need to implement strong data encryption, secure transport protocols, and use trusted encryption keys and certificates when transmitting sensitive information.
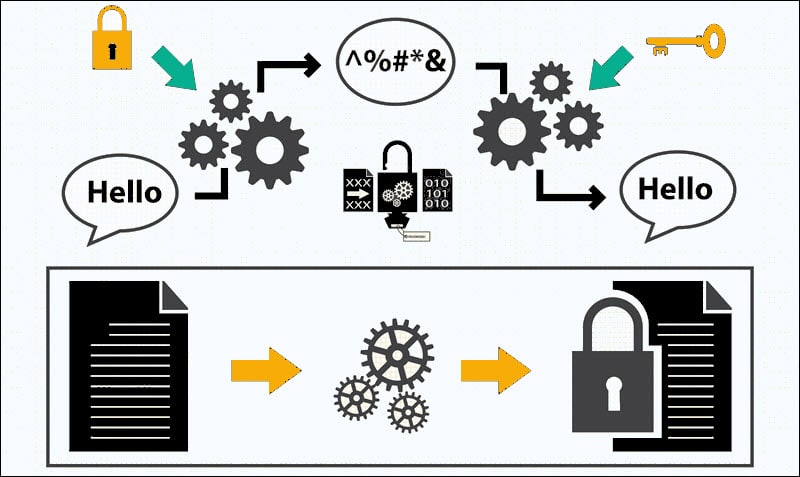
The procedures and policies for encrypting cardholder data transmissions must be well documented and accessible so that employees can reference the documentation when necessary.
Merchants also need to create and enforce rules that prohibit employees and end-users from sharing personal account numbers (PAN) and other cardholder and authentication data using emails, chat services, or other open communication channels.
Use and Routinely Update Anti-Virus Software
Countless viruses and other malicious programs regularly target businesses that process online payments. All system components need to be protected by automated anti-virus software that is active 24/7.
New viruses, attack vectors, and exploits are discovered every day, making it imperative to update and upgrade anti-virus solutions consistently. Trained staff should also review anti-virus logs and keep track of known exploits and malicious software.
Develop and Maintain Secure Systems and Applications
Merchants should refer to websites specializing in online security, reliable news outlets, and official vendor pages to learn about possible system vulnerabilities and how to protect against these newly discovered security threats.
It is essential to classify potential threats into different categories (high-risk, medium risk, and low risk). This way, merchants can prioritize which vulnerability to address first and decide how to allocate resources adequately.
All systems should always be up to date and patched with the latest security patches. Before implementing new applications, any development or test account users need to be removed.
Restrict Access to Cardholder Data
User accounts that have access to cardholder data are a potential liability. Merchants should keep the number of employees with such privileges to a minimum.
It is vital to provide access only to employees that could otherwise not complete their work-related tasks. For example, a risk assessment officer may need to review cardholder data, but there is little reason to award the same privileges to a website designer.

Systems should automatically deny access and log any attempt by unauthorized users to access protected data.
Assign a Unique ID to Each Person With Access
By assigning a unique ID to each user, organizations can track who accesses cardholder data, for what purpose, and if any changes were made. This allows businesses to impose personal responsibility for individual actions and easily register, follow, and limit security breaches if they occur.
By assigning unique IDs to each user, merchants can:
- Lock accounts after a certain number of unsuccessful login attempts.
- Revoke access for terminated or inactive users.
- Require re-authentication if a user is idle for a certain period.
Merchants should implement additional security features such as two-factor authentication to improve data security.
Restrict Physical Access to Cardholder Data
Potential attackers can quickly utilize unattended workstations and exposed wireless access points to introduce vulnerabilities into the network.
Physical access to devices that contain or can be used to retrieve cardholder data needs to be restricted. Businesses should control who can enter their premises using employee pass-cards, PIN codes, biometric scans, or other facility entry controls. Different rules need to be devised for specific employee roles, visitors, and temporary staff.

Dedicated staff should maintain a current device registry and regularly inspect company hardware to detect unsanctioned devices.
Track and Monitor Access to Network Resources and Cardholder Data
Once a security issue occurs, it is imperative to react quickly and build a clear picture of the events that led to data being compromised. To track and thoroughly analyze events, merchants need to implement a system activity log.
An automated system that registers every individual activity regarding cardholder data is essential for controlling the aftermath of a security breach.
Audit trails need to be able to correlate individual user accounts, their actions, and system components that handle cardholder data.
Data breaches are often discovered much later than they occurred. Merchants should keep historical log records on hand for analysis for at least a year before deleting them.
Routinely Test Security Systems and Processes
Penetration testing and vulnerability scans are invaluable for detecting system exposure and potential weaknesses in network architecture. Using the services of an Approved Scanning Vendor (AVS), certified by the PCI SSC, helps merchants identify vulnerabilities and forestall potential security breaches. Scans should be performed regularly and repeatedly until all vulnerabilities have been addressed.
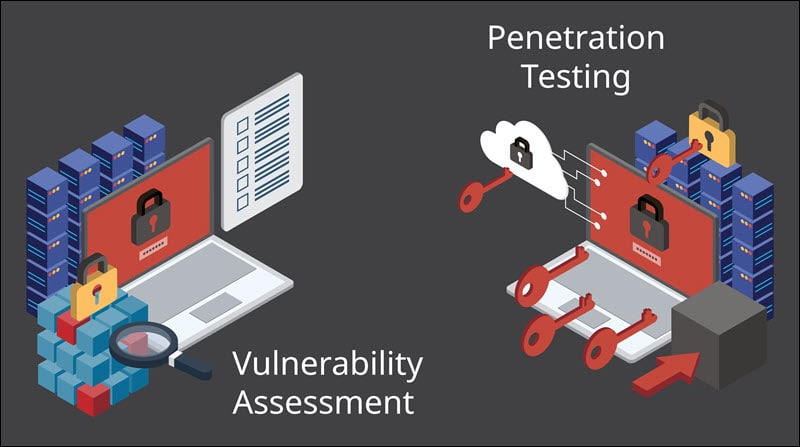
Wireless network connections are especially vulnerable and are commonly used to extract sensitive customer information. It is vital to keep an up-to-date inventory of authorized access points and create clear procedures on how to proceed if a rogue wireless access point is detected.
Implement and Maintain an InfoSec Policy for All Personnel
An information security policy needs to outline data protection and training procedures for employees that handle cardholder data. Appropriate training materials and courses should reflect the latest standards in data protection.
Staff should recognize potential threats and understand how their actions can aid or prevent attacks. They need to know how to react when an attack is identified and how to handle the consequences of a successful breach.
Designated staff should be available around the clock to cut reaction times and immediately initiate damage control procedures.
Note: Check out our in-depth PCI compliance checklist.
Benefits of PCI Compliance
PCI data security standards have several clear benefits for merchants that accept card payments:
- Businesses only need to comply with a single set of standards to process payments for all major card brands.
- Merchants receive clear guidance for strengthening their network architecture and security protocols.
- System components are always up to date.
- Staff receives regular training and clear instructions on preventing and dealing with attempted security breaches.
- Merchants establish a good working relationship with banks, payment processors, card brands and maintain a good reputation in the payments industry.
- By meeting PCI DSS requirements, merchants are well-positioned to implement other payment compliance regulations.
Challenges of PCI Compliance
Complying with PCI requirements is not without challenges:
- PCI requirements are extensive, detailed, and complex. Merchants with limited resources and staff can have difficulty fulfilling the necessary preconditions.
- Creating a PCI-compliant environment requires a significant investment of money and time. The initial costs of getting PCI compliant can be offset by using the services of an established payment processor, web host, and other third-party software providers.
- PCI compliance dramatically reduces but does not eliminate the chances of a data breach.
- Compromised data negatively impacts customers, merchants, financial institutions, and card brands. A data breach can result in a permanent loss of reputation, the ability to process card payments, and card issuer and government fines.
Conclusion
Merchants who accept card payments and collect personally identifiable data from their customers are responsible for protecting that data. They need to learn about potential security threats and do everything they can to protect their businesses and customers from such attacks.
Complying with PCI standards is a good starting point to create and maintain a secure environment for all the participants in the payment process
