Introduction
Passwords should ideally be long, complex, and unique. At the same time, passwords need to be easy to remember, and a customer ought to create a new password for every website or service they sign up for.
It can be challenging to strike the right balance and apply password requirements without negatively affecting the customer’s experience. An overly strict password policy can annoy customers and significantly increase abandonment rates. A lenient password policy is a security risk.
Learn about the best password practices for ecommerce websites and keep your customers safe and satisfied.

Why do Ecommerce Websites Need a Password Policy?
Humans cannot memorize long and complex character strings. Common and short passwords are easy to guess by using brute force attacks and dictionary-based algorithms.
Despite well-documented flaws, the authentication process on most websites is heavily reliant on customer passwords due to several factors:
- Passwords are free.
- Businesses do not need to invest in sophisticated authentication systems.
- Customers have an intuitive understanding of how passwords work.
- Password authentication systems are easy to scale regardless of the number of users.
Ecommerce companies need to establish policies that prevent unsafe passwords and motivate their customers to create strong credentials. Comprehensive password policy best practices include:
- A minimum password length requirement.
- Account lockout after several incorrect login attempts.
- Reasonable password complexity rules.
- Blocklists that prevent the use of dictionary terms, usernames, names of website services, and compromised passwords.
- An onscreen password-strength meter.
- Not insisting on periodic password changes.
Applying these requirements increases password strength and has minimal impact on customer satisfaction.
Best Ecommerce Password Policies
Imposing complex passwords for services that do not contain personally identifiable information can be a source of frustration for customers.
Before introducing the suggested policies, determine the level of threat for your business model and the type of service you provide. For example, customers are willing to put in additional effort to create strong passwords for essential services and websites that hold sensitive personal information.
1. Minimum Password Length
Longer passwords are harder to guess. Require your customers to use a minimum of 8 characters when choosing their passwords.
Advise customers to create long passwords and even use whole passphrases if possible. Allow for the use of special characters and spaces.
Particularly long passwords (measured in MB) can affect the performance of underlying systems and strain the password hashing process. You should implement a reasonable restriction for password length.
A maximum length of 64 characters enables customers to create exceptionally strong passwords.
2. Account Lockouts and Delays
Counter brute-force attacks by locking out accounts after several unsuccessful login attempts. The limitation should permit legitimate users to make mistakes but not allow too many attempts that can result in an attacker guessing the password. The allowed number of failed attempts should not exceed 10 failed logins.
The number of failed attempts can be lower if you apply additional verification systems such as:
- Setting up CAPTCHA before authentication.
- Configuring increasing time-out periods between failed login attempts.
- Whitelisting customers’ IP addresses.
- Using other authentication tools such as geolocation, browser metadata, and other analytics tools to authenticate customers.
- Avoid using secret questions that help customers remember their passwords.
Ensure that your system disregards previous failed attempts once the customer’s credentials and IP address are successfully verified.
Note: In case you need to block certain IPs in your Magento store, check out our tutorial How To Block an IP Address in Magento.
3. Block Dictionary Words, Usernames, and Compromised Passwords
Maintain blocklists of unacceptable passwords and regularly update their indexes.
Many cyberattacks try to guess passwords using algorithms based on dictionaries. It is vital to prevent customers from using words found in dictionaries as passwords.
Note: Implementing an 8-character password minimum means you only need to include dictionary words that meet that criteria.
Strictly prohibit the use of usernames and passwords that have been compromised in known security breaches and passwords derived from the website’s services. There are numerous online databases like Have I Been Pwned that can assist with maintaining up-to-date records.
Merely blocking certain words and passwords is not enough. Ensure that the customer always receives onscreen feedback about why their choice is not acceptable and instructions on how to create a secure password.
4. Password Complexity
Forcing consumers to include upper-case letters, special characters, and numbers in their passwords has not produced the expected results. Complex passwords with different character types are more secure but harder to remember and use.
Customers are regularly exasperated when online services reject their password choices. As a result, users have resorted to predictable patterns. Instead of “iloveyou”, the user can enter “Iloveyou1!” and create a formally acceptable password.
Attackers target frequently used character sequences and mangle password variations making this requirement highly susceptible to attack.
Insisting on complex passwords has also led customers to write down or unsafely store passwords, severely reducing their value.
To improve password complexity, website owners need to encourage customers to use password managers. Some of the most prominent password managers include LastPass, KeePass, 1Password, and Dashlane.
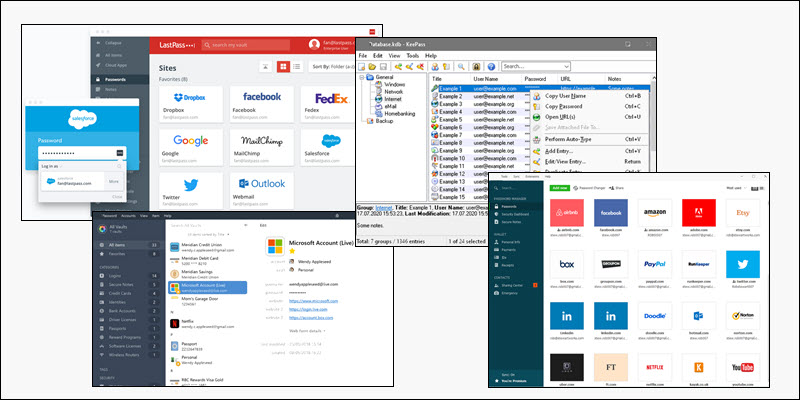
Allow customers to paste passwords to streamline the use of password managers and passphrases.
5. Use an Onscreen Password-Strength Meter
The initial registration and password update pages should contain onscreen password-strength meters. Preemptive password checkers evaluate the content and changes in the password field and calculate the chosen password’s strength.
The strength meter needs to meaningfully explain why certain passwords are not acceptable and provide guidance on how to create strong passwords.
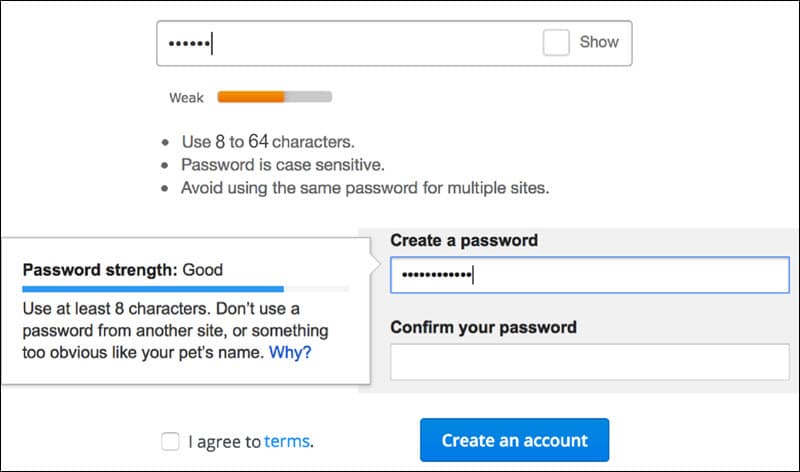
This proactive approach also discourages customers from slightly tweaking passwords if their initial weak password is rejected. The goal is to motivate customers to willingly create robust passwords.
Customers forget passwords all the time. Do not insist on hidden characters (dots or asterisks). Allow customers to see their password while typing. To streamline password creation on mobile devices, display each character for a short time to allow customers to verify their entry.
6. Mandatory Password Changes
It has been standard practice to require password changes in predefined periods, for example, every 90 or 180 days. There is no conclusive evidence that this process significantly increases password security.
When prompted, users tend to change their passwords only marginally and use similar patterns. It also increases the pressure on users by forcing them to devise and memorize many passwords. A much better approach is to monitor compromised passwords and ask customers to change passwords only if there is a known issue with their current password.
Additional Password Policy Considerations
Insisting on intricate and complex passwords frustrates customers and is counterproductive. Users are going to find ways to avoid restrictions and compromise password strength in the process.
More advanced techniques and tools that take some of the pressure away from the end-user are a better choice. Blocklists, secure hashed storage, login rate limiting, customer education, and advanced authentication tools are available even to small business owners.
Keep in mind that attacks associated with passwords are not only affected by password complexity and length. Social engineering, phishing, and logging keystrokes are attack techniques that work regardless of the password’s strength.
It is necessary to combine password protection with other sophisticated methods, such as two-factor authentication, risk-based authentication, address-based checks, and behavioral analytics.
Conclusion
Use the policies outlined in this article to improve password strength and increase overall security on your ecommerce website.
Helping customers understand why they need strong passwords and how to create one is an essential component of a comprehensive password policy.
We recommend checking out our article on ecommerce website security to learn more about how to secure your online business.
